In today’s threat environment, data centers can no longer rely on a single perimeter or isolated control to safeguard critical infrastructure. Instead, the industry has increasingly adopted the concept of concentric security circles, also known as layered defense-in-depth, as a foundational design and operational strategy. This model establishes multiple, progressively restrictive zones of protection that surround the facility’s most critical assets, ensuring that threats are deterred, detected, delayed, and ultimately defeated long before they can reach sensitive systems.
The outermost security circle typically begins at the property boundary. This layer focuses on early deterrence and situational awareness through perimeter fencing, anti-ram vehicle barriers, controlled vehicle entrances, lighting, and wide-area surveillance. By establishing clear territorial control and monitoring activity at the site edge, security teams gain valuable response time and visibility into potential threats before they approach the building itself. The Uptime Institute notes that strong perimeter controls remain one of the most effective ways to reduce unauthorized access attempts and improve incident response across mission-critical facilities.¹
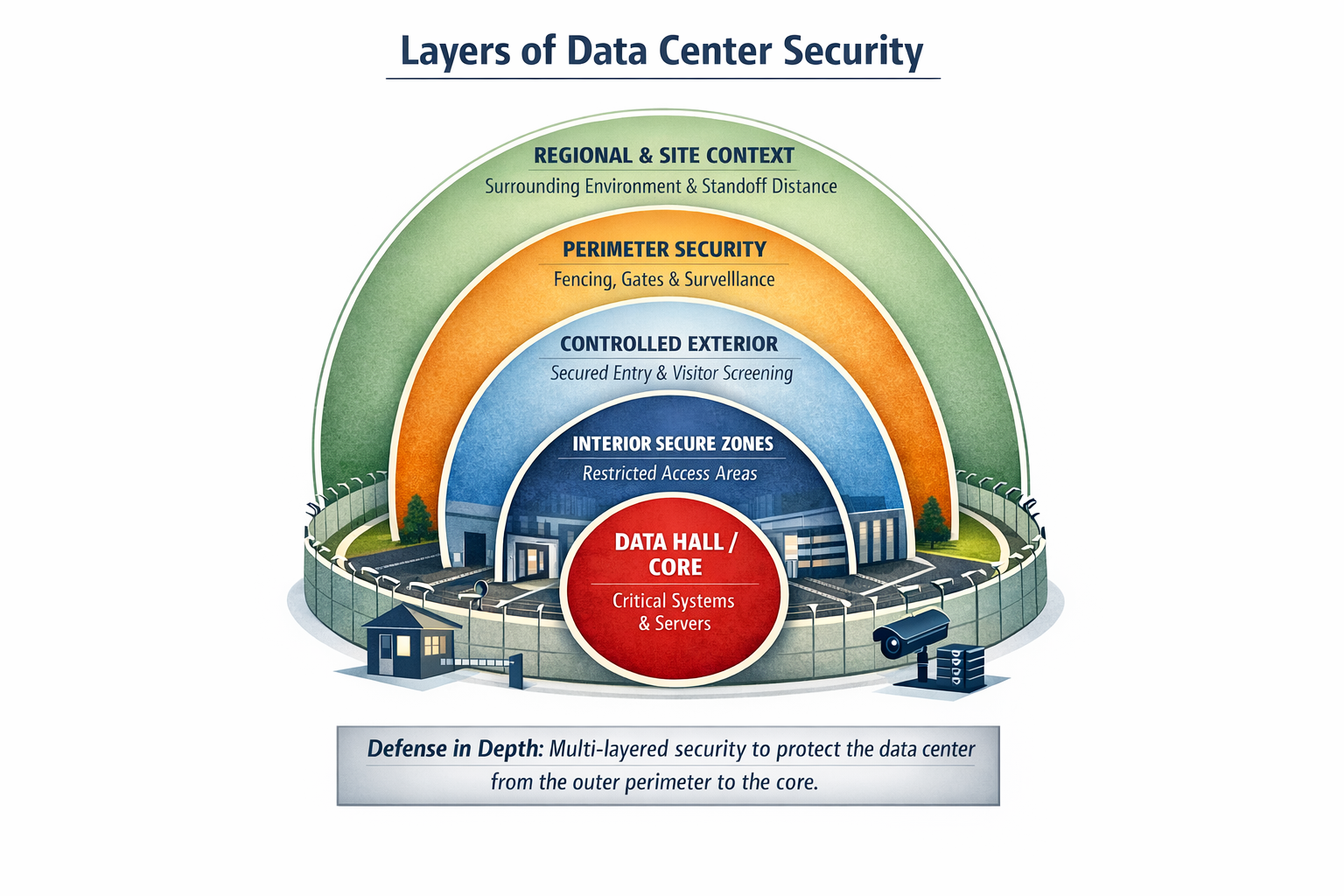
Moving inward, the next circle often includes controlled access to the building and its immediate surroundings. Guard stations, visitor management systems, credential verification, and monitored entry points ensure that only authorized individuals can proceed beyond the exterior shell. This layer is particularly important in mitigating risks associated with contractors, vendors, and third-party service providers—one of the most common vectors for both physical and cyber-related incidents in data centers.² By enforcing strict access procedures and escort policies, organizations create accountability while reducing the likelihood of insider threats or accidental exposure.
Inside the facility, additional concentric layers protect specific operational zones such as data halls, network operation centers, power rooms, and control systems. These inner rings often rely on increasingly robust authentication measures including proximity badges, biometrics, mantraps, and role-based access controls. Surveillance systems with intelligent analytics monitor movement patterns, tailgating attempts, and abnormal behavior in real time. According to the Open Compute Project’s physical security guidelines, segmentation of interior spaces combined with layered authentication significantly strengthens overall resilience by preventing lateral movement within critical environments.³
At the core of the concentric model lies the most sensitive infrastructure, the servers, storage systems, and operational controls that support digital services, national infrastructure, and economic stability. By the time an individual reaches this innermost circle, they should have passed through multiple independent security controls, each designed to verify authorization and detect anomalies. This cumulative effect ensures that no single failure compromises the entire system, aligning with widely accepted principles of defense-in-depth across both physical and cybersecurity disciplines.⁴
In Data Center Security: The Blueprint for Resilient Infrastructure, Christopher Hills expands the concentric security circles concept beyond physical barriers alone, positioning it as a holistic framework that integrates physical protection, cybersecurity, governance, commissioning, and operational culture into one cohesive defense strategy. Rather than viewing each layer as a standalone measure, the book demonstrates how resilient facilities align perimeter controls, access management, surveillance, cyber monitoring, and policy enforcement into a unified system designed to scale with evolving threats. Drawing from real-world projects, including hyperscale data centers, global security operations centers, and critical infrastructure deployments, Hills illustrates how layered security not only reduces risk but also improves accountability, uptime, and long-term operational resilience.
The concentric model also plays a vital role in regulatory compliance and industry standards. Frameworks such as NIST SP 800-171, ICD-705 for sensitive facilities, and integrated testing practices outlined in NFPA 4 all emphasize the importance of layered controls and coordinated system performance.⁵ Security is no longer judged solely by the presence of cameras or fences, but by how well each layer works together as part of a continuously tested and monitored ecosystem.
Ultimately, concentric security circles transform the data center from a passive structure into an active defensive environment—one that anticipates threats, limits exposure, and responds dynamically to risk. As data centers continue to underpin everything from healthcare and finance to government operations and AI infrastructure, layered security is no longer optional; it is a fundamental requirement for digital trust and national resilience. As Hills argues in The Blueprint for Resilient Infrastructure, the most secure facilities are not those with the most technology, but those designed with integrated, layered defenses that treat security as a system rather than a product.
- Uptime Institute, Data Center Security: Reassessing Physical, Human, and Digital Risks (New York: Uptime Institute Intelligence, 2023).
- Verizon, 2023 Data Breach Investigations Report (New York: Verizon Enterprise, 2023).
- Open Compute Project, OCP Physical Security Guidelines for Data Centers (Open Compute Project Foundation, 2022).
- National Institute of Standards and Technology (NIST), Security and Privacy Controls for Information Systems and Organizations, SP 800-53 Rev. 5 (Gaithersburg, MD: NIST, 2020).
- National Fire Protection Association, NFPA 4: Standard for Integrated Fire Protection and Life Safety System Testing (Quincy, MA: NFPA, 2021); National Institute of Standards and Technology, Protecting Controlled Unclassified Information in Nonfederal Systems and Organizations, SP 800-171 Rev. 2 (Gaithersburg, MD: NIST, 2020).





